The fundamental idea of the quantum computing and communications has been introduced by Stephan Wiesner when she introduced the principles of numerous developments in quantum computing and cryptography field in 1970. She presented the fundamental concept of the no-cloning theory which states that the quantum information can’t be replicated [1].
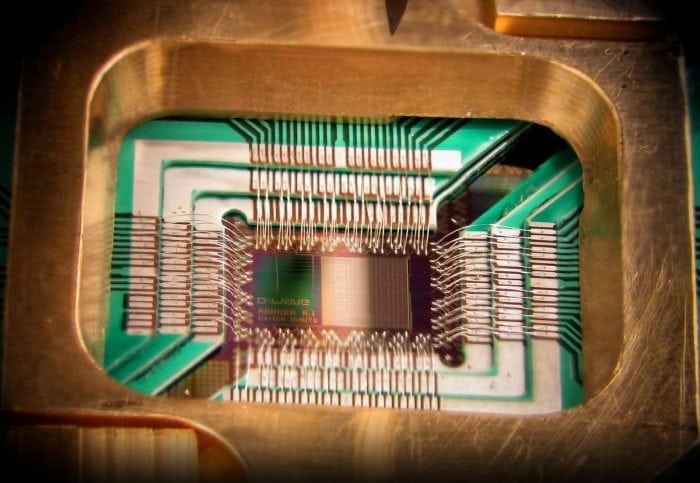
Contrasting to the classical computer, the quantum computer can enhance the substantial processing ability and achieve many tasks by applying all prospective transformations simultaneously. Furthermore, the architecture of quantum computers is contradictory from the classical one which is controlled by a number of transistors. The data can be represented as bits (0 or 1) in the classical environment.
On the other hand, the quantum environment represented the data represented as quantum bits and in a superposition state. The superposition state denotes that the quantum state can be 0, 1 or in both states simultaneously. Quantum computers reveal hypothetical relationships with non-deterministic and probabilistic computers [2, 3, 4]. Ever since the seminal work of Bennett and Brassard [1], the field of quantum cryptography has evolved rapidly. Quantum cryptography verifies its unconditional security [2–5] by the no-cloning theorem [6]. A number of approaches and models have used quantum Cryptography to secure communication processes between two and various participants [7–13].
The security and confidentiality of the communication process achieved an immense benefit by utilizing the properties of quantum mechanics compared to the perspective classical one. The most significant characteristic of quantum computing is entanglement. Entanglement is one of the distinctiveness physical properties that explain the way of how the photons can be interrelated to each other irrespective of the distance.
The verification of user identity through entanglement has been proposed by many research groups. Regrettably, some of the proposed protocols have been failed form the security viewpoint as the attacker can attain some of the transmitted sequences of the photons and transmit the remained to the destination over the quantum channel. Consequently, the probability of information disturbance is increase as the attacker can retrieve a portion of the transmitted trustworthy message. In the viewpoint of the limitations of the current protocols, a new protocol for authentication of the user identity by utilizing the property of entanglement especially Greenberger–Horne–Zeilinger (GHZ) states, which cause the proposed protocol is more efficient and secure compared to some of the proposed protocols is introduced in [18].
According to various aspects, the proposed protocol proved its adequacy and worthiness. First, by exploiting the principle of states, the proposed protocol is more secure as the eavesdropping of any transmitted single photon can disrupt the communication among the communicated users compared to other protocols which utilize the principle of EPR pair to verify and transfer the private messages among the communicated users. Unfortunately, these protocols present an error and ineffective transfer of the photons. This happens in case of the sender transfers a series of photons with the chance of the eavesdropper to capture some of them and carry out a measurement. Therefore, the probability of information loss is rising as the eavesdropper can retrieve some of the transmitted secret messages.
Secondly, the number of authenticated users is increased as a result of applying a large Hilbert space ( states). Accordingly, we maximize the potential ability for the applications of quantum communication and cryptography. Thirdly, the security analysis of the authentication processes of the proposed protocol — compared to different types of attacks — proved that it is unconditionally secure and that the eavesdropper will not reveal any information about the transferred key and the eavesdropper introduces an error possibility irrespective of the sequence of the measurements.
The proposed protocol achieves both the maximal security and efficiency of the transmission, which is apparent from two aspects: first, the state is the maximally entangled state, so that the correlation can be more easily destroyed once any single N particle is attacking; secondly, using the particle makes eavesdropping detection more effective and secure, in comparison to some of the other protocols. The presented work opens the door to maximize the application range for quantum communication and authentication like Quantum Block-Chain.
These findings are described in the article entitled Robust general N user authentication scheme in a centralized quantum communication network via generalized GHZ states, recently published in the journal Frontiers of Physics. This work was conducted by Ahmed Farouk and M. Elhoseny from Mansoura University, J. Batle from Universitat de les Illes Balears, M. Abdel-Aty from Sohag University, Mosayeb Naseri from the Islamic Azad University, Muzaffar Lone from the University of Kashmir, Alex Federov from the Russian Quantum Center, Majid Alkhambashi from the Al-Zahra College for Women, and Syed Hassan Ahmed from Kyungpook National University.
References:
- Wiesner, S. (1983). Conjugate coding. SIGACT News, 15(1), 78- 88.doi:10.1145/1008908.1008920
- Nielsen, M., & Chuang, I. (2000). Quantum computation and quantum information. Cambridge: Cambridge University Press.
- Zeng, G.H. (2006) Quantum cryptology : Science Press
- Van Assche, G. (2006). Quantum cryptography and secret-key distillation. Cambridge: Cambridge University Press.
- C. H. Bennett and G. Brassard, Quantum cryptography: Public key distribution and coin tossing, Theor. Comput. Sci. 560, 7 (2014)
- M. Nielsen and I. Chuang, Quantum Computation and Quantum Information, Cambridge: Cambridge University Press, 2000
- G. H. Zeng, Quantum Cryptology, Beijing: Science Press, 2006
- G. Assche, Quantum Cryptography and Secret-Key Distillation, Cambridge: CambridgeUniversity Press, 2006
- M. S. Sharbaf, Quantum Cryptography: A New Generation of Information Technology SecuritySystem, Sixth International Conference on Information Technology. Nevada, USA, IEEE, pp 1644–1648, April, 2009
- W. K. Wootters and W. H. Zurek, A single quantum cannot be cloned, Nature 299(5886), 802(1982)
- A. Poppe, M. Peev, and O. Maurhart, Outline of the SECOQC quantum-key distribution networkin Vienna, Int. J. Quant. Inf. 06(02), 209 (2008)
- M. Peev, et al., The SECOQC quantum key distribution network in Vienna, New J. Phys.11(075001), 1367 (2009)
- C. Elliott, Building the quantum network, New J. Phys. 4, 46 (2002)
- C. Elliott, A. Colvin, D. Pearson, O. Pikalo, J. Schlafer, and H. Yeh, Current status of the DARPA quantum network, Quantum Information and Computation 5815, 138 (2005)
- A. F. Metwaly, M. Z. Rashad, F. A. Omara, and A. A. Megahed, Architecture of multicast centralized key management scheme using quantum key distribution and classical symmetricencryption, Eur. Phys. J. Spec. Top. 223(8), 1711 (2014)
- A. Farouk, M. Zakaria, A. Megahed, and F. A. Omara, A generalized architecture of quantumsecure direct communication for N disjointed users with authentication, Sci. Rep. 5(1), 16080 (2015)
- M. Naseri, M. A. Raji, M. R. Hantehzadeh, A. Farouk, A. Boochani, and S. Solaymani, A schemefor secure quantum communication network with authentication using GHZ-like states and cluster states controlled teleportation, Quantum Inform. Process. 14(11), 4279 (2015)
- Farouk, Ahmed, J. Batle, M. Elhoseny, Mosayeb Naseri, Muzaffar Lone, Alex Fedorov, Majid Alkhambashi, Syed Hassan Ahmed, and M. Abdel-Aty. “Robust general N user authentication scheme in a centralized quantum communication network via generalized GHZ states.” Frontiers of Physics 13, no. 2 (2018): 130306.