Many agronomic systems could be at risk considering short-term climate changes, but the numerous processes at stake and their interactions are still hard to predict. Among all, tree crops such as coffee, cacao, or peaches are the most affected by these changes because their perennial growing cycle makes it difficult, long, and often expensive to adapt their production to new conditions.
Therefore, there is an increasing need for information to better predict future climate change impacts on perennial crops and forests to design new agricultural and silvicultural practices to cope with these changes before they occur. However, changes in climate conditions lead to complex combinations of effects on the water and carbon balances of ecosystems, and can thus, potentially, affect agro-ecosystem production. For example, coffee tree growth and fruit production are particularly sensitive to high temperatures and water availability, and previous studies often predict future huge losses of production or area cover.
Nevertheless, shade provided in agroforestry systems could mitigate the effects of climate changes under different management options, but in turn, could increase the competition for light and water resources. Studying these processes and their interactions is then the first step towards new agricultural and silvicultural practices adapted to future changes in temperature and rainfall patterns.
Process-based models (PBMs) are generally well suited to address these challenges. PBMs apply our understanding of fundamental physical and ecophysiological processes to mechanistically simulate systems (Bohn et al., 2014). PBMs often use the soil-plant-atmosphere continuum (SPAC, Philip (1966)) formalism. This continuum describes the interactions of the processes that occur between the main domains (soil, plant, and atmosphere) to represent the ecosystem status in terms of coupled water and energy flows. In these complex systems, all component status is important to model as each one drives the flows from the others through water potentials, water phases and available energy (Lobet et al., 2014; Manzoni et al., 2013).
The energy amount incoming to a component depends on the available energy coming from the atmosphere and on the ecosystem properties as material emissivity, transmissivity, absorbance, or canopy structure. The absorbed energy is the source of all potential change in temperature and in the phase of the water within or at the surface of an object, triggering evaporation and transpiration. This absorbed energy will also interact with the surrounding air through conduction (i.e. sensible flux) and vapor (i.e. latent fluxes), increasing its temperature and humidity.
The water and energy balance also interact with the carbon cycle. Indeed, plants harvest a part of this energy to make carbohydrates molecules from atmospheric CO2 diffusing through their stomata. By doing so, intercellular water from the stomata evaporates (i.e. transpiration), leading to more negative local water potential and pulling water from the roots, and then from the soil. To avoid desiccation, stomata conductance can be adjusted by plants depending on the microclimate near the leaf which depends on the energy balance of the system; and on the leaf water potential, that is directly connected to the soil water status itself.
By controlling the fluxes of carbon into plants, energy and water balance drive plant growth — the only sink of carbon from the atmosphere to all life in the ecosystem. By controlling temperature, they also drive respiration, which is a source of carbon towards the atmosphere. Thus, the SPAC formalism is complex because it requires a great amount of knowledge on the physical and physiological properties of the system, but is necessary to properly simulate the transpiration, leaf and soil evaporation, and energy budget.
Among all agro-ecosystems, perennial plantations and forests are probably the most complex to model because they tend to have heterogeneous canopies. This is especially the case for agroforestry systems such as Coffea arabica plantations (Figure 1) because the light distribution and the micrometeorological conditions are highly isotropic (i.e. they are spatially heterogeneous), so two individual plants from the same field can experience very different conditions. Hence, a tree-scale 3D model must be used to better integrate the spatial complexity while modeling these systems.

Figure 1. Coffea arabica plantation in agroforestry under Erythrina poeppigiana shade tree in Aquiares, Costa Rica. Source: F. Beilhe & O. Roupsard.
The MAESPA model (Figure 2) is a 3D explicit process-based model (Duursma and Medlyn, 2012) that simulate forests energy, water, and carbon fluxes at individual-scale. It is particularly suited to simulate agroforestry system because it describes the forest at voxel scale, which is a homogeneous representation of a certain volume element of the tree crown. It can manage several tree species with their own position on the plot, their structure (crown height, width…), and their physical and physiological parameters.
The model computes a fine estimation of the light interception, energy, water, and carbon fluxes for each plant in the forest and for the soil while considering the canopy spatial heterogeneity, which makes it a relevant candidate for addressing effects of climate change upon horizontally heterogeneous forest systems. However, it has been shown in previous studies that MAESPA tends to under-estimate high evapotranspiration rates on Coffea agroforestry systems, and on Pinus and Eucalyptus stands. Preliminary investigations suggested that this phenomenon arises from an unreliable estimation of the canopy temperature and vapor pressure.
In a recent article, Vezy et al. (2018) modified the MAESPA model to better simulate the evapotranspiration rates thanks to a refined representation of the canopy micro-climate by including a computation of both within-canopy air temperature and within-canopy vapor pressure (Figure 2). Since both variables result from and in turn affect complex interactions in the canopy, the soil, and the atmosphere, their inclusion is a critical improvement to the MAESPA model.
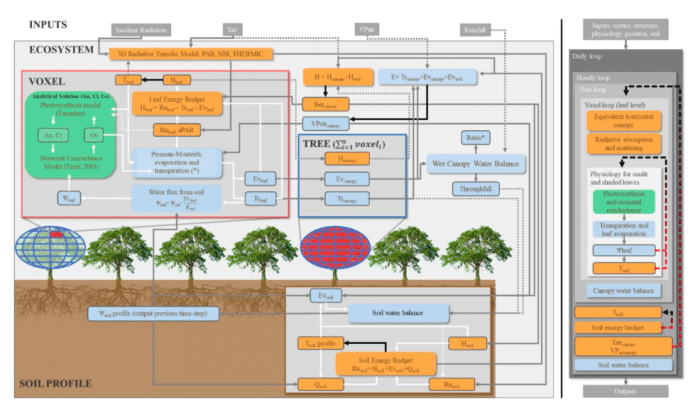
Figure 2. Detailed MAESPA model workflow. Some calculations are made at the voxel scale (VOXEL, in red) before being summed for upscaling to tree level (TREE). Other calculations are made directly at the ecosystem level (ECOSYSTEM) such as the soil energy budget and the water balance. Voxel-scale photosynthetic module is represented in green, energy modules (or variables) in orange and water-related modules (or variables) in blue. Black arrows emphasize the variables that are optimized. Linear workflow is shown on the right side, showing the three iterative computations with arrows. (*): A ratio of dry/wet canopy is used at voxel scale for evaporation and transpiration partitioning. Republished with permission from Elsevier from: https://doi.org/10.1016/j.agrformet.2018.02.005
This work led to an improvement of the simulation of canopy temperature by MAESPA (Figure 3), which in turn led to better water and energy fluxes simulations afterward (not shown, see the article for more details on model evaluation). The authors then used MAESPA to model the evapotranspiration of different tree crops with increasing spatial heterogeneity, from a simple homogeneous monospecific Eucalyptus stand to a complex agroforestry Coffea plantation with two shade tree species.
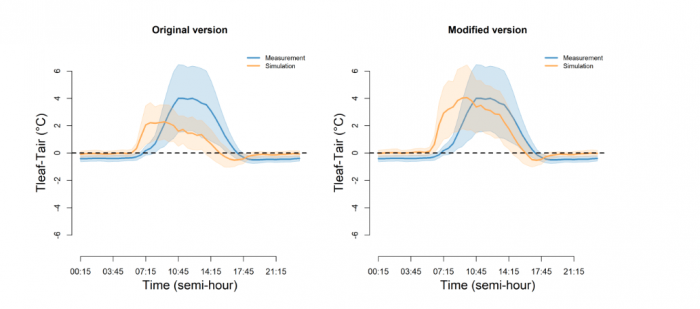
Figure 3. Average (line) and standard deviation (polygon) of the diurnal time course of the canopy and air temperature difference simulated using the original version of MAESPA (left) or the modified version from the Vezy et al. (2018) article (right) compared to IR100 measurement along a period range starting from 13-03-2015 until 12-03-2016 in a Coffea plantation under full-sun management in CATIE, Costa Rica. Republished with permission from Elsevier from: https://doi.org/10.1016/j.agrformet.2018.02.005
The authors found that the evapotranspiration from the Eucalyptus plantation located in the Sao Paulo state in Brazil was higher in 2012 than the total yearly precipitations of the same year (Figure 4) because it transformed almost all incoming solar radiation into latent heat fluxes (i.e. evapotranspiration). These results reveal that intensive Eucalyptus plantations could reduce water resources at landscape scale under lower precipitations regimes, which could be increasingly problematic under climate change as climate models forecast less rainfall in these regions in the future.
A second interesting result is that the shaded trees in the Coffea agroforestry system in Costa Rica help to transform more incoming solar energy into latent fluxes, changing the microclimate experienced by the Coffea below into a cooler, more-humid one with less intense radiation. As a result, the Coffea leaf temperature and transpiration were reduced. Consequently, agroforestry could be a potential tool to adapt Coffea cropping systems to climate change, by reducing the negative effect of increasing air temperature on coffee yield. More investigation on the potential to reduce Coffea leaf temperatures by shade is needed, but these results could guide future research on these aspects.
A third interesting result was that the agroforestry management had a high impact on the way precipitation was recycled back into the ecosystem, either to the atmosphere or to the soil water stock. The higher the shade tree density over Coffea plants, the higher the evapotranspiration, hence making more water recycling back into the atmosphere. These phenomena are important to understand because shade trees could become very competitive for water resources under dryer climates, especially for high-density agroforestry systems. Hence, MAESPA could be used to investigate the optimal shade tree species, their optimal density, and their optimal management considering local pedo-climatic conditions.
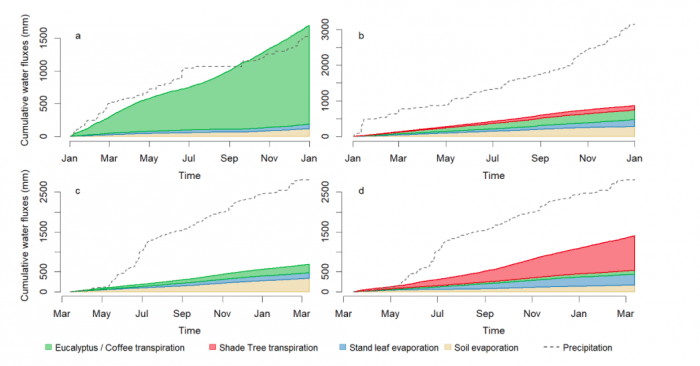
Figure 4. Cumulated simulated evapotranspiration partitioning and cumulated precipitation for a a) homogeneous Eucalyptus stand (year 2012), b) Coffea Aquiares AFS plantation with low density of E. poeppigiana (year 2011), c) Coffea CATIE full-sun management (one year starting the 2015-03-13) and d) Coffea CATIE grown under high density C+E shade trees (same period than c). Republished with permission from Elsevier from: https://doi.org/10.1016/j.agrformet.2018.02.005
These findings show that the MAESPA model is a good candidate to investigate the relationships of the processes involved in water and energy balances, especially for cropping systems with complex canopy structure. The model can be used to assess the management with the best partitioning between soil and leaf evaporation versus plant transpiration considering the local pedo-climatic conditions. MAESPA is also well suited to predict ecosystem responses to climate changes thanks to its process-based functioning and could be used on other plant species or regions.
These findings are described in the article entitled Measuring and modelling energy partitioning in canopies of varying complexity using MAESPA model, recently published in the journal Agricultural and Forest Meteorology. This work was conducted by Rémi Vezy, Mathias Christina, Olivier Roupsard, Yann Nouvellon, Remko Duursma, Belinda Medlyn, Maxime Soma, Fabien Charbonnier, Céline Blitz-Frayret, José-Luiz Stape, Jean-Paul Laclau, Elias de Melo Virginio Filho, Jean-Marc Bonnefond, Bruno Rapidel, Frédéric C. Do, Alain Rocheteau, Delphine Picart, Carlos Borgonovo, Denis Loustau, and Guerric le Maire.